Digital or Technology- Facilitated Abuse
Digital or technology-facilitated abuse is a form of abuse that uses phones, social media, email, tracking tools, apps, or other technology to monitor, harass, threaten, control, or intimidate someone. It can happen in current or former relationships and often overlaps with stalking, coercive control, emotional abuse, and financial abuse.
-
Digital abuse may include:
Repeated threatening or harassing texts, calls, emails, or messages.
Tracking someone’s location through apps, shared accounts, spyware, or GPS.
Monitoring social media, passwords, or online activity.
Sharing private images, messages, or information without consent.
Impersonation, account hacking, or using technology to isolate or intimidate someone.
Coercing someone to send sexual images or using digital tools to shame, pressure, or blackmail them.
-
Digital harassment: Repeated unwanted texts, calls, emails, or messages meant to scare, control, or overwhelm someone.
Stalking and surveillance: Tracking a person’s location, monitoring their social media, checking their phone, or using apps, spyware, GPS, or smart devices to watch them.
Image-based abuse: Sharing, threatening to share, or secretly creating intimate images or videos without consent. This includes revenge porn and deepfake sexual images
Sextortion: Threatening to expose intimate images unless the person meets demands, sends more images, or gives money.
Hacking and account takeover: Accessing someone’s email, phone, social media, or banking accounts without permission.
Impersonation and doxxing: Creating fake accounts, pretending to be someone else, or sharing private information to embarrass, threaten, or isolate them.
Device and home-tech control: Using smart locks, cameras, doorbells, or other connected devices to monitor or restrict a person’s movements.
Coercive control through technology: Demanding passwords, forcing constant check-ins, limiting who someone can contact, or using technology to isolate them from support.
-
Digital abuse can feel constant because it can follow a person anywhere through their phone or online accounts. It may also spill into offline harm by affecting work, school, safety, relationships, and mental health. Because technology is so embedded in daily life, survivors may have to think carefully about safety, privacy, and access before changing passwords or accounts.
-
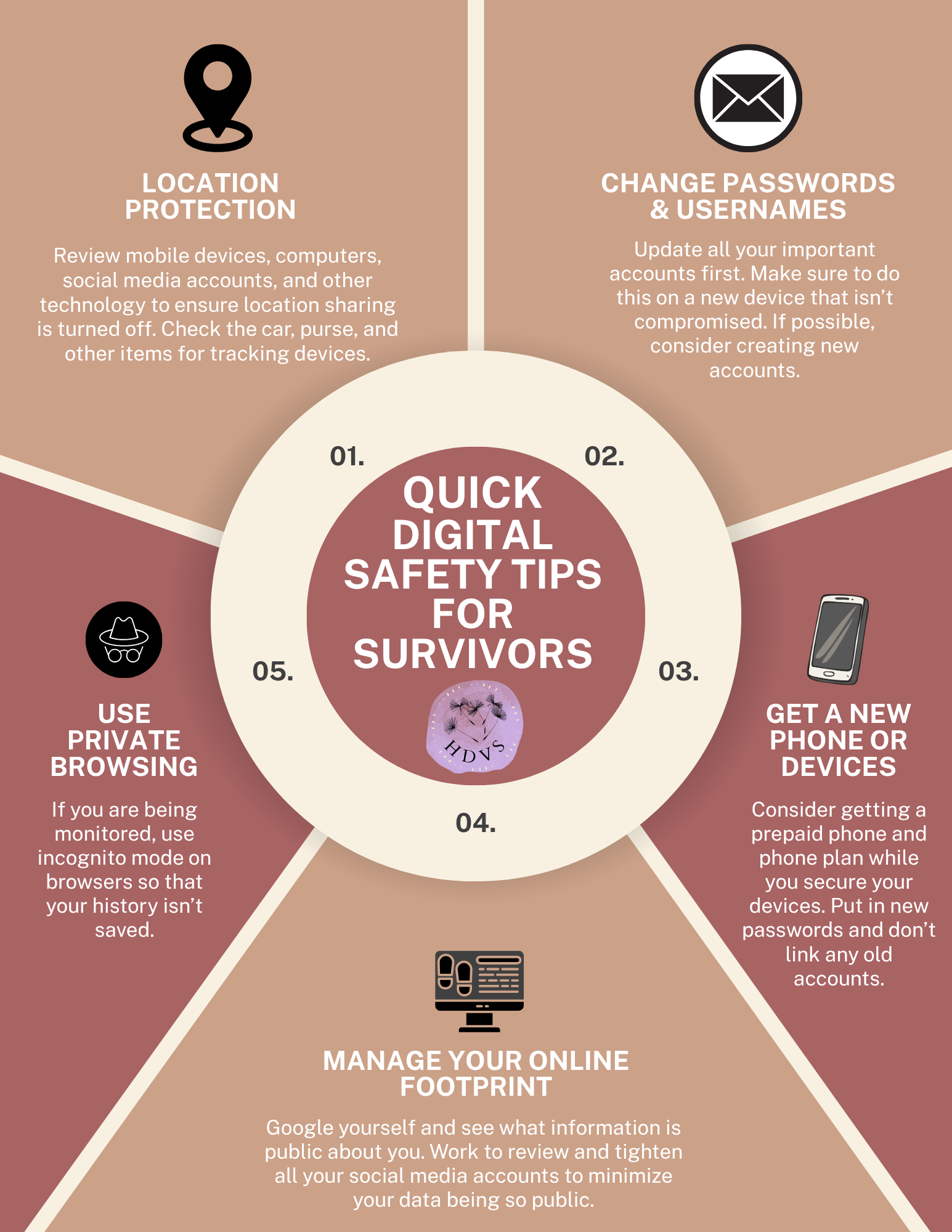
Using a safer device, such as a library computer or a trusted friend’s phone, when seeking help.
Changing passwords and creating new ones that the abusive person cannot guess.
Reviewing location settings, shared accounts, and device access to limit tracking.
Checking whether spyware, shared cloud accounts, or connected devices may be revealing private information.
Saving evidence of abusive messages, stalking, or harassment in a safe way.
Thinking through safety before removing devices, blocking someone, or closing accounts, because those actions can sometimes escalate risk.